Security Researcher Unlocks Hidden Hard Drive Firmware Hacks for Xbox 360 Exploits
Breaking: Researcher Reveals Hard Drive Firmware Vulnerabilities Enable Xbox 360 Hacks
A security researcher known as [I Code 4 Coffee] has disclosed a method to reverse-engineer and modify hard drive firmware, exploiting previously undocumented backdoor commands to compromise Xbox 360 consoles. The breakthrough, detailed in a technical report published on GitHub, exposes critical flaws in how hard drives handle vendor-specific instructions.
"Most people never think about hard drive firmware as an attack surface," said Dr. Elena Voss, a cybersecurity analyst at CyberLabs. "This work shows that even the deepest layers of storage hardware can be manipulated for malicious or research purposes."
Background
The research began with four storage devices: three standard hard drives and one solid-state drive (SSD). The researcher sought existing documentation on modifying hard drive firmware but found scarce and outdated resources, as there is little mainstream demand for such modifications.
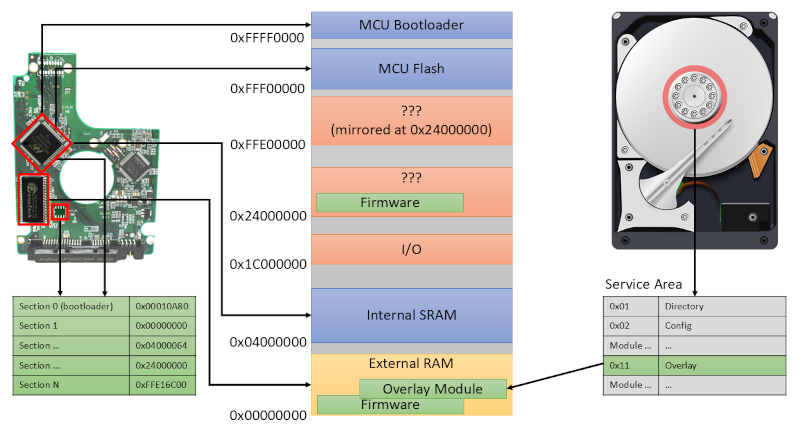
Key tools included a PC-3000 data recovery system, which provided firmware dumps, and access to diagnostic RS-232 ports on certain drives. Additionally, the study leveraged JTAG interfaces to bypass normal firmware restrictions.
What This Means
This discovery opens a new vector for console modding and security research. By altering hard drive firmware, attackers could potentially execute unauthorized code on Xbox 360 consoles, bypassing built-in protections.
"The presence of backdoor vendor commands is alarming," commented Marcus Yang, a hardware security engineer at SecureTech. "These commands are often left in for manufacturing diagnostics but can be repurposed if the firmware is exposed."
Technical Details
The reverse-engineering process involved analyzing firmware dumps for undocumented command sets. The researcher identified multiple "backdoor" vendor commands accessible through the hard drive's serial interface.
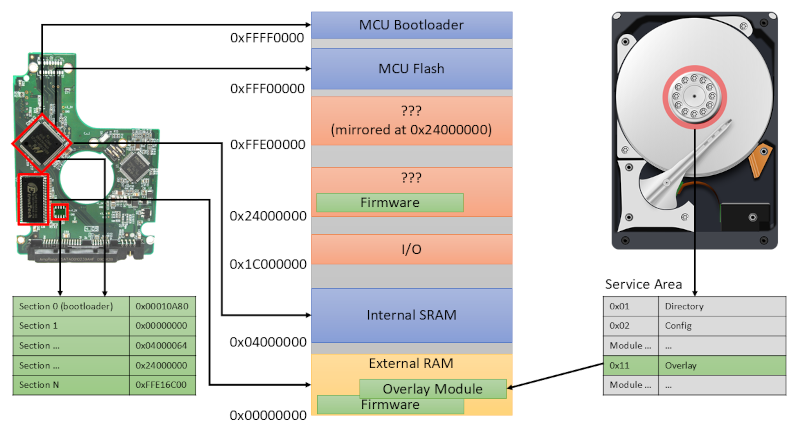
GitHub repositories now host the technical artifacts, including firmware dumps and scripts to test similar vulnerabilities on other drives. The researcher notes that the RS-232 port provides a direct line into the drive's inner operations, while JTAG offers a more invasive method for firmware manipulation.
Expert Reactions
"This is a wake-up call for the storage industry," said Dr. Voss. "Manufacturers need to audit their firmware for hidden features that could be exploited." The findings have already sparked discussions within the security community about the broader implications for data integrity and device security.
Some cybersecurity experts caution that the techniques may require specialized hardware and deep technical knowledge, limiting their immediate real-world impact. However, the research demonstrates that hard drive firmware is not as immutable as commonly assumed.
Next Steps
The researcher plans to release additional tools and documentation to help others replicate the work safely. Meanwhile, Xbox 360 enthusiasts may soon see new homebrew applications that leverage these firmware hacks.
For more details, visit the project's GitHub page to access the technical artifacts and firmware dumps.
Related Articles
- Critical Authentication Bypass in cPanel & WHM: What You Need to Know About CVE-2026-41940
- Cybersecurity Experts Sentenced for Role in BlackCat Ransomware Attacks: Key Questions Answered
- Cybersecurity Consultant Demand Surges as Global Cybercrime Costs Exceed $10 Trillion Annually
- Linux Kernel Releases 7.0.6 and 6.18.29 Address Critical Dirty Frag & Copy Fail 2 Vulnerability
- 6 Critical Lessons from the KICS and Trivy Supply Chain Attacks of 2026
- Cybercriminals Paralyze Canvas Platform as Ransom Deadline Looms Over 275 Million Users
- Uncovering a Botnet Operated by a Brazilian DDoS Protection Firm
- Meta's Enhanced Encryption: A Deeper Look into Backup Security